Overview
Sectigo Connector for Java ("the connector") is a certificate management solution for automating the enrollment and management of SSL/TLS certificates on Java servers. The connector imports the provisioned certificates into a Java KeyStore (JKS) on a remote or local server. Communication with a remote server occurs through an embedded SSH client. SCM credentials can be stored in plaintext or encrypted form.
Once the certificate is in the JKS, you will be able to do the following:
-
SSL/TLS Communication: JKS is commonly used to store SSL/TLS certificates for securing HTTPS connections in Java-based web servers like Tomcat, Jetty, WebLogic, and WebSphere.
-
Java Applications Authentication: Applications use JKS to store private keys and certificates for authentication purposes, such as signing data or verifying identities.
-
Client-Server Authentication: In mutual TLS authentication, both client and server use JKS to store and manage their SSL certificates and private keys.
-
Java Cryptography API (JCE/JCA): JKS is used within Java applications for cryptographic operations such as encryption, decryption, and digital signatures.
-
Spring Boot & Microservices: Secure communication in microservices architectures often involves JKS for managing SSL certificates in Spring Boot and Spring Security.
-
Database Security: Some databases (like Oracle) allow storing SSL keys and certificates in JKS to enable encrypted connections.
The following certificate types are supported:
-
Domain Validation (DV): Single-domain, multi-domain, and wildcard certificates issued by Sectigo
-
Organization Validation (OV): Single-domain, multi-domain, and wildcard certificates issued by Sectigo
-
Extended Validation (EV): Single-domain and multi-domain certificates issued by Sectigo
-
Private SSL: Private SSL certificates issued by Sectigo
The following key types are supported:
-
RSA: RSA-2048, RSA-3072, and RSA-4096
-
ECDSA: ECDSA-256 and ECDSA-384
Audience
This guide is intended for IT administrators and system administrators who have knowledge of IT security, cloud security, and are also familiar with Sectigo Certificate Manager (SCM).
Scope
This guide covers instructions on using the Sectigo REST API to enroll certificates, save them locally, and import them into a Java KeyStore on a remote server.
Architecture
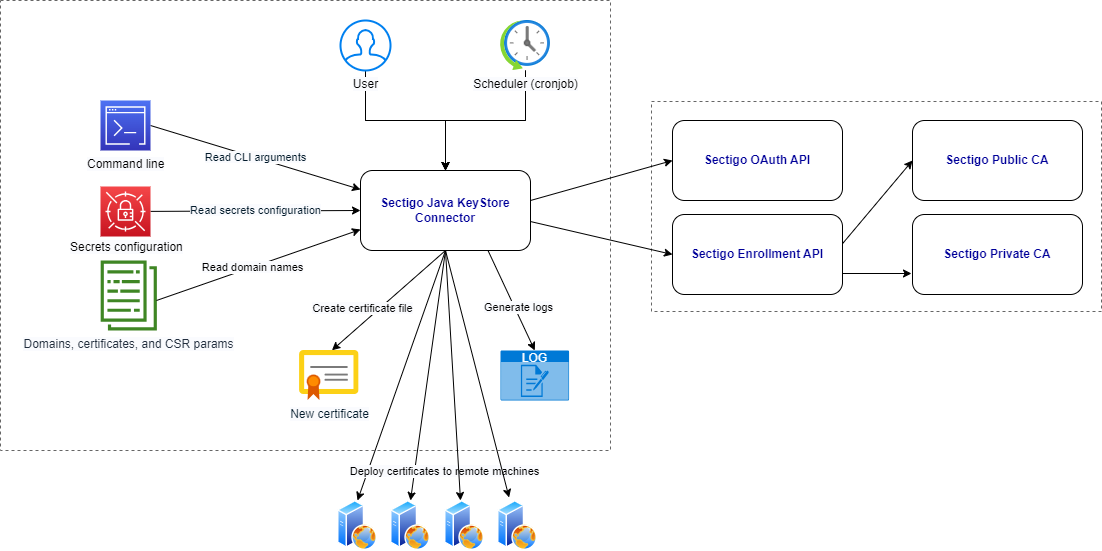
Execution workflow
During execution, the connector does the following:
-
Reads the
certificates.yamlfile(s) from the./domainsdirectory and its subdirectories (if any) to get the certificate enrollement information. -
Generates a key pair and a CSR on the local machine.
-
Sends the CSR with an enrollment request to SCM.
-
Downloads the entire certificate chain in the CRT format to the local machine.
-
Saves the certificate name and ID to the
cache.csvfile on the local machine. -
Imports the certificate into a Java KeyStore (JKS) file on the local machine.
-
Sends the JKS file to the remote machine through SSH.
-
Deletes the temporary files, such as the CRT and JKS files, from the local machine.
Package contents
The package contains the following components:
-
domains: This directory and it subdirectories store the
certificate.yamlfiles.-
certificates.yaml: This file contains certificate enrollment information: CSR parameters, renewal window, and more. The
certificates.yamlfile can reside in the./domainsroot directory or you can copy it to subdirectories for specific domains.
-
-
configs: This directory stores the SCM credentials and remote machine credentials files.
-
scm.yaml: This file contains the SCM credentials.
-
servers.yaml: This file contains essential details about the remote (or local) machine.
-
-
SCM Client EULA v1.0.1.txt: The EULA agreement. You need to accept it when you run the connector for the first time.
-
sectigo-java-agent: The connector in the form of a binary executable file.